
Your keys, your funds, with disaster recovery options.
Retain complete
control of your funds, establish stringent
spending rules, all without the typical risks of loss.
Liana provides recovery options
in the event of key
loss, employee turnover, or third-party failures. These recovery options are safeguarded by time
locks, enforced by the Bitcoin network.

No vendor lock-in, it’s a Free Open Source Software!
Liana is free to use, even in a business environment. Its source code is transparent and is maintained by both a community of contributors and the Wizardsardine company. There's no vendor lock-in, making integrations and modifications easy.

Easier operational security for your organization
Not every employee can be trusted to store their backups securely. With Liana, you can time-lock backups to prevent leaks, establish disaster recovery paths to avoid loss, and assess and enforce your organization's security without making compromises.
A team of Security Experts available to help.
The Wizardsardine team can assist you in defining the most appropriate setup for your specific situation, guide you through the deployment process, and provide ongoing support. We offer full packages with contractual Service Level Agreements for your convenience.
CONTACT USLiana offers unprecedented security and resilience with novel features.
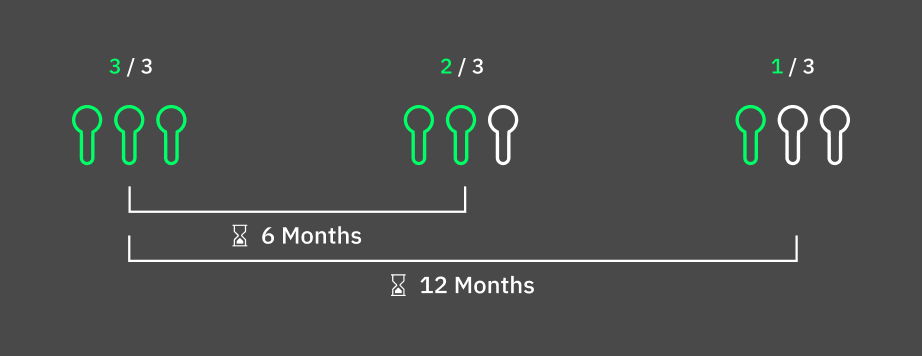
Decaying Multisig
This model reduces the threshold of signatures over time to mitigate for some keys to be lost without locking the funds forever. As long as the wallet is used, the spending conditions are strict. If no transaction is signed for a long time, the threshold reduces to allow for recovery.
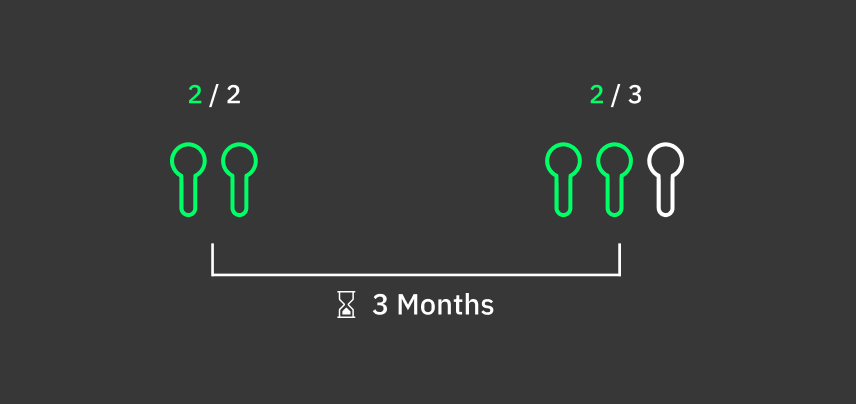
Expanding Multisig
This model does not reduce the number of keys required, instead it increases the pool of keys able to sign. This allows for example to have a recovery key held by the board of directors, only valid in case of a deadlock between the funders. These keys can also be held by third parties such as custodians, without sacrificing self-custody unless a timelock expires.
Safer Backups
The backup mnemonics can be timelocked, drastically the risk of theft and break ins. As long as an access to a backup key is detected before expiry of its timelock, the attacker cannot steal funds.

A combination of these tools can make your institutional wallet more secure against theft, and resilient to loss than the regular semi-custodial or multisig enterprise wallet.
CONTACT US
The ultimate protection against loss
Professional key agents who will be able to recover your funds as a last resort, should everything else fail.
Know more about safety net
